Podcast Summary
The Rise and Fall of Mt. Gox: The Importance of Securing Digital Assets in Bitcoin: While Bitcoin offers a decentralized digital currency alternative, the Mt. Gox incident emphasizes the need for secure storage and monitoring of digital assets, as the cryptocurrency gains mainstream attention.
Bitcoin is a decentralized digital currency that operates via crowdsourcing transactions, enabling anonymous but transparent payments without the need for physical cash. Mt. Gox, the first Bitcoin exchange, dominated the market, processing over 70% of all Bitcoin transactions. However, in 2014, Mt. Gox shut down, announcing that 750,000 Bitcoins worth over $450 million were stolen. The nature of Bitcoin's complicated technological architecture has made it challenging for authorities to track down the stolen funds. While Bitcoin has numerous features that make it an attractive alternative to traditional currencies, the Mt. Gox incident highlights the importance of secure storage and monitoring of digital assets, especially as Bitcoin and other cryptocurrencies continue to gain mainstream attention.
Investigating the Downfall of Mt. Gox.: Despite the transparency of the blockchain, poor implementation can still lead to issues and hacking attempts. In-depth analysis and efficient searching methods can help in determining the causes of a system failure.
The blockchain is a public record that stores every Bitcoin transaction and is anonymous, while virtual wallets store Bitcoins. Mt. Gox, a Bitcoin exchange, had issues with Liberty Reserve withdrawals due to poorly implemented code allowing hackers to withdraw more than they should. The founder of Mt. Gox, Jed McCaleb, personally created the site. Kim Nilsson, a software consultant, investigated Mt. Gox's downfall and spent three years piecing together the almost 40 gigabytes of transaction data. It was hard to determine a single satisfying answer, as there were a lot of things that went wrong. Kim's technical analysis helped him to investigate the data with efficient searching methods and additional information from the CEO of Mt. Gox.
Vulnerabilities and Insolvency in Cryptocurrency Exchanges: Strong security protocols and proper management are crucial for preventing thefts and insolvencies in cryptocurrency exchanges. Failing to do so can have disastrous consequences for both the exchange and its customers.
The vulnerabilities in Liberty Reserve led Jed McCaleb to sell Mt. Gox to Mark Karpel's at a favorable price, but things started to go downhill with the loss of 80,000 bitcoins from the hot wallet. When Mark took over, he was faced with a lot of missing money and insolvency issues due to inadequate management. Later, Mark stored 300,000 bitcoins on his unsecured personal computer, which was stolen by a thief, who later returned 297,000 bitcoins for a small keeper's fee. This incident shows the importance of strong security protocols and better management in cryptocurrency exchanges to prevent thefts and insolvencies.
Mt. Gox and the Importance of Cybersecurity for Cryptocurrency Platforms: Strong cybersecurity measures are vital for any online platform dealing with valuable assets. A proactive approach towards cybersecurity, constant monitoring, and upgrading of security measures is crucial to prevent breaches and protect users and the market.
Mt. Gox faced multiple breaches that resulted in loss of Bitcoins and compromised user data. These breaches led to the crash of Bitcoin's price that impacted users and the market. The incidents highlight the importance of strong cybersecurity measures, especially for platforms dealing with cryptocurrencies. Despite facing setbacks, Mark Karpel believed in turning around Mt. Gox and expanding its reach to Europe. However, the breaches continued, and the attackers aggressively altered account balances and wiped accounts, making it challenging to track the evidence. Mt. Gox's experiences underline the need for a proactive approach towards cybersecurity and the importance of constant monitoring and upgrading of security measures for any online platforms dealing with valuable assets.
Security Breaches and Bitcoin Theft: Lack of secure codebase and encryption techniques in Mt. Gox led to the siphoning off of Bitcoins, incentivizing hacking. Amateur codebase and patchy security protocols were major reasons leading to loss and theft of Bitcoins.
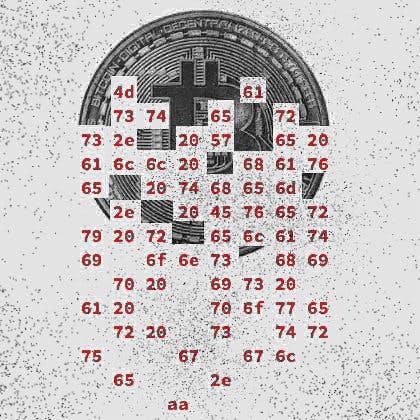
The security breaches in Mt. Gox led to the siphoning off of 650,000 Bitcoins, mainly due to the lack of a secure codebase and encryption techniques. Bitcoin incentivized hacking by making it easier for hackers to steal actual money just by hacking computers. Amateur codebase and patchy security protocols were the main reasons behind the technical errors that led to the loss of 45,000 Bitcoins and destruction of 2,500 Bitcoins. Though Mt. Gox pioneered the online cryptocurrency market, it was never a professional exchange, and its lack of secure software and systems made it easy for hackers to breach the system and steal Bitcoins.
The downfall of Mt. Gox and its ongoing legal battles.: Transparency and following regulations are essential for businesses to maintain credibility and prevent financial loss.
Mt. Gox, once the largest Bitcoin exchange, faced security breaches and thefts causing them to become insolvent, and ultimately shut down. The owner, Mark, tried to keep these breaches hidden and keep the reputation of Mt. Gox intact. He also ran a trading bot called the Willy Bot, which resulted in losing an additional $50 million and 22,000 Bitcoins. Mt. Gox gave $5 million to a company called CoinLab to handle all North American transactions, but the deal went bad and CoinLab filed a lawsuit against Mt. Gox seeking $75 million. Mt. Gox was also in violation of acting as an unregistered money transmitter in the US and had $5 million seized by the US Department of Homeland Security.
Lessons learned from the Mt. Gox bankruptcy: Keep Bitcoin on your own computer and use reliable exchanges with good reputations. Keep technology up to date and actively trade rather than leaving Bitcoin on an exchange.
The Mt. Gox bankruptcy taught the industry and community important lessons about Bitcoin security. It's best to keep a Bitcoin wallet on your own computer that you control for long-term storage, and to choose reliable exchanges that adhere to strict audits and have a good reputation. Leaving Bitcoin on an exchange is not a good idea unless you're actively trading it. Mt. Gox's losses also highlight the need for best practices and keeping technology up to date within the industry. Mark Karpeles, who still has 200,000 Bitcoins from the bankruptcy, is currently undergoing legal proceedings and owes his creditors $450 million, while his Bitcoins are now worth $2 billion.