Podcast Summary
The Expertise of Lisa Forte in Managing Insider Threats: Companies must implement insider threat programs and take security seriously to prevent insider-related security incidents, which can be as sophisticated as ransomware attacks. Experts like Lisa Forte can help navigate and mitigate these threats.
Insider threats are a major problem for companies, particularly for music venues, sports stadiums, and theatres where people try to get in for free by using insider help. Lisa Forte, a partner at Red Goat Cyber Security, started her career in security as a lawyer for private security companies, helping them identify legal ways to protect cargo ships from pirate attacks. She later moved into the operations side of things to help boats secure themselves from pirates. Her expertise in managing risks and developing insider threat programs can be valuable to companies who want to avoid insider-related security incidents. Pirates have become as sophisticated as ransomware groups in the cybersecurity space, which means companies need to take security seriously and stay ahead of potential threats.
Protecting Ships from Pirate Attacks: When protecting ships from pirate attacks, various methods can be used including barbed wire, welded internal doors, citadels, water cannons, and Long-Range Acoustic Devices (LRADs) that warn approaching ships to stay away.
To protect ships from pirate attacks, barbed wire can be put up, internal doors can be welded shut, a citadel can be built, water cannons can be installed, and LRADs can be used. LRADs are Long-Range Acoustic Devices that can warn approaching ships to stay away and can pump out noises up to 160 decibels, making them a powerful sound weapon. They were invented after the USS Cole attack in 2000, and they are often used by shipping companies to help protect their ships from potential attacks.
Use of Technology and Armed Guards for Protection of Cargo Ships Against Threats: Cargo ships face dangerous waters and increasing piracy threats. Technology and armed guards are critical for self-defense, but force escalation is sometimes unavoidable. Quick thinking is necessary, as pirates develop rapidly with ransom payments.
The use of technology like earplugs and LRADs have become necessary for cargo ships passing dangerous waters to protect themselves and repel suspicious boats without using force. However, pirates have developed sophisticated tactics, and cargo ships have to escalate force, such as water cannons and warning shots in unavoidable cases. Armed guards onboard the ships became mandatory, who were trained to use lethal force as an absolute last resort. During an attack, the ship's team raised the level of force to protect themselves from approaching boats. While it is crucial to have a plan in case of attacks, incidents will hit hard and require figuring out things on the fly. The pirates' tactics developed rapidly due to well-funded resources from ransom payments.
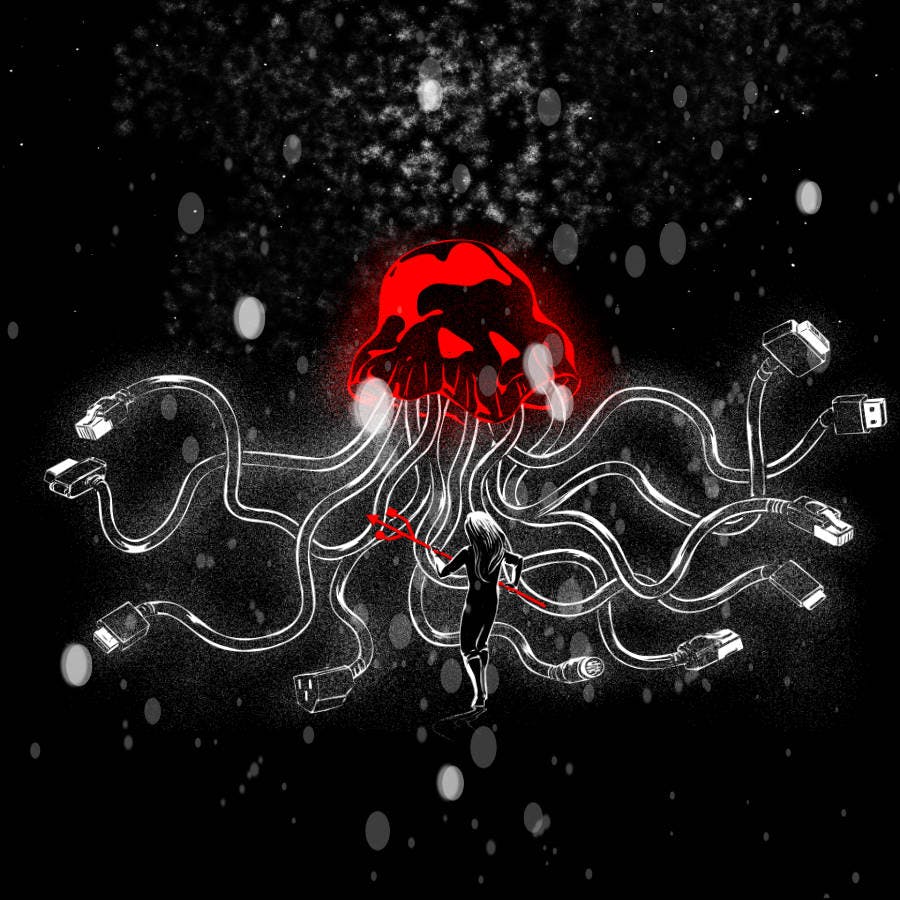
Asymmetry in Cybersecurity: Insider Threats and the Battle for Online Security: Defenders in cybersecurity are at a disadvantage due to the asymmetry in the battle against attackers who don't play by the rules. Insider threats pose a significant danger, but companies can develop effective programs and responses against it with the help of specialized cybersecurity firms like Red Goat.
Attackers don't play by the rules, while defenders have to abide by the law, creating an asymmetry in the battle and how companies secure themselves online. Insider threats in cybersecurity are a significant danger as it involves trusted individuals within the company who might attack it, ultimately leading to a breach. LinkedIn has become a social network that scientists and professionals use to connect, share, and post content, leading to insider threats, like in the case, where an employee exchanged e-mails with someone who shared common interests and had access to sensitive information. Lisa started her Cybersecurity company, Red Goat, and specializes in cybersecurity crisis exercises, including addressing insider threats, helping companies develop programs and responses against it.
Preventing Insider Threats in Companies: Companies should be cautious during employee recruitment, employees must be aware of data protection regulations, and both parties should take necessary measures to avoid exfiltration of private information. Data security is everyone's responsibility.
Insider threat is a common data breach in companies, especially when private information is exfiltrated by an employee. Companies should be cautious while recruiting new employees, and employees should also be aware of their actions while working in a company. Sharing proprietary information of a company can lead to severe consequences for both the employee and the company. It is essential to understand the rules and regulations of a company related to data protection and intellectual property. Employees should avoid sending sensitive information through emails and other easily accessible platforms. Data security is the responsibility of everyone associated with the company, and therefore, it is vital to create awareness and take necessary measures to prevent insider threats.
The Dangers of Unsolicited Job Offers and Sharing Sensitive Information: Be cautious of unsolicited job offers and never share sensitive information without verifying the identity of the requester. Disable user accounts immediately if suspicious activity is detected. Always be vigilant and cautious in communication with unknown individuals or companies.
The story highlights the dangers of responding to unsolicited job offers and sharing sensitive information in response to them. In this case, a fake LinkedIn profile lured a scientist into downloading malware on his work device, which could have given the attackers access to sensitive company information. The attack was likely either industrial/corporate espionage or the work of nation state actors. This incident also emphasizes the importance of disabling user accounts as soon as suspicious activity is detected. Such cyber attacks should serve as a reminder to always be vigilant and cautious when communicating with unknown individuals or companies, whether it be through social media or email, especially when asked to share sensitive information.
Beware of Cyber Attacks through LinkedIn: Exercise Healthy Paranoia & Limit Personal Info Shared Online. Avoid Using LinkedIn's Direct Messaging Feature and Be Cautious of Profile Posts and Comments.
Nation state-level cyber attackers are using LinkedIn to social engineer employees of targeted companies to gain access to valuable intellectual property or to install malware. This vulnerability is due to the abundance of personal information that LinkedIn provides about an individual and their employer. While it is important to have an online presence, it is essential to exercise healthy paranoia and limit personal information shared online. LinkedIn's direct messaging feature is particularly risky since anyone with a LinkedIn Premium account can direct message any user. However, turning off direct messages may not be enough to prevent attackers from accessing personal information, as anyone can still comment on profile posts and deduce email addresses from names and employers.
The dangers of fake profiles on social media: Be cautious of strangers on social media, especially those who share many similarities and interests with you, as they may have malicious intentions and seek to exploit your trust. Always verify information before taking any action.
Beware of fake profiles on social media. The woman was tricked by a fake Peruvian girl on Facebook chat who gained her trust by having fake similarities and mirrored all her interests from a wide-open Facebook profile. The fake woman built trust over time and friendship with text conversations and approached the woman to expose an environmental scandal at their workplace. The woman was horrified after hearing about the unsafe conditions caused by their company in Peru and decided to quit her job. The fake woman suggested exposing the issue to a journalist. In the end, both the victim and fake woman left the situation after providing all the documents required to the investigative journalist.
Balancing Employee Privacy and Security Against Insider Threats: Companies should invest in educating employees about insider threats while respecting their privacy, in addition to staying vigilant about social engineering tactics used by attackers. A balanced approach can help protect against attacks without breaching employee privacy rights.
Insider threats are a real danger for companies and investing in training employees about these dangers is essential. However, some companies make the mistake of implementing Draconian monitoring measures on staff, which is not recommended. In this case, the attackers preyed on the victim's passion for the environment and used it against her to leak sensitive company documents. This lady was manipulated into believing that she had real friends who were silenced by their employer. Companies can protect themselves from such attacks by adopting a balanced approach that does not breach employees' privacy rights. Additionally, the human element can never be disregarded, and companies should stay vigilant about educating their staff to be aware of social engineering tactics used by attackers.
Importance of a positive work environment in preventing insider threats.: Investing in employee assistance programs and building a supportive work culture can reduce the risks of insider threats. Security measures should include prevention, detection, remediation, and investigation of attacks, and not just perimeter defense.
Invest in employee assistance programs to identify and address employee struggles and create a supportive work environment to prevent insider threats. Happy and loyal employees are less likely to sabotage their employer. Security measures should not only focus on prevention but also on detection, remediation, and investigation of attacks to minimize damage. Building a perimeter defense is not enough, as companies have to be ready to respond to attackers and assess the extent of the compromise. The example of a secret city in Soviet Russia proves that content and privileged employees are more likely to keep agreements and be loyal to their employers. Creating a positive work culture is essential to reduce the risk of insider threats.